Threat Watch
Rapidly assess your cybersecurity health with Threat Watch for instant insights on compromised accounts and devices.
Visit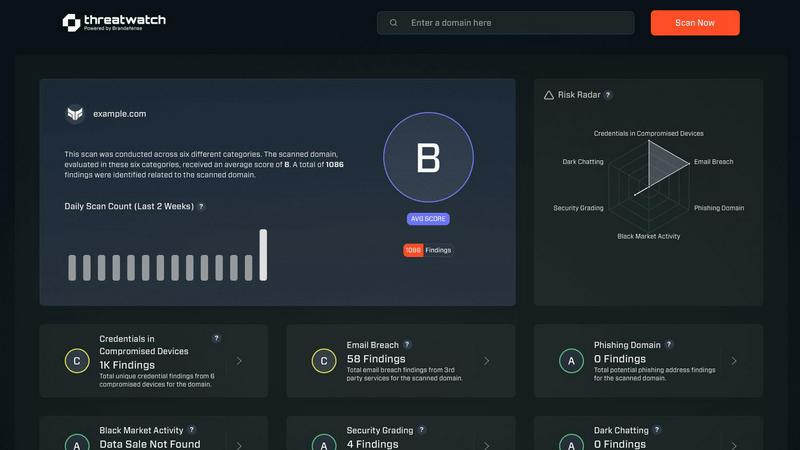
About Threat Watch
Threat Watch is your organization’s lightning-fast command center for cybersecurity intelligence, designed to provide an immediate, crystal-clear view of your digital security posture. This unified platform continuously analyzes your assets, vulnerabilities, and exposures across the surface, deep, and dark web. By transforming complex threat data into actionable insights, Threat Watch empowers IT leaders, security teams, and business executives to move at the speed of risk. Its core value proposition lies in speed and efficiency, enabling users to identify critical risks in real-time and prioritize them based on actual business impact. With Threat Watch, organizations can execute mitigation strategies faster than threats can evolve, automating the heavy lifting of cyber threat intelligence. From detecting compromised employee credentials and breached accounts to identifying phishing addresses and vulnerable devices, Threat Watch saves you the most valuable resource—time—ensuring your cybersecurity health is always a priority.
Features of Threat Watch
Real-time Risk Assessment
Threat Watch delivers real-time risk assessments by continuously monitoring your organization’s digital footprint. This feature ensures that you are always aware of your current security posture, allowing for quick responses to emerging threats.
Comprehensive Threat Intelligence
With comprehensive threat intelligence, Threat Watch aggregates data from the surface, deep, and dark web. This feature enables users to gain insights into potential vulnerabilities and threats, transforming raw data into meaningful action plans.
Automated Credential Monitoring
Automated credential monitoring scans for compromised employee credentials and breached accounts, alerting your security team instantly. This proactive feature helps mitigate risks associated with unauthorized access and data breaches.
Vulnerability Detection and Reporting
Threat Watch provides robust vulnerability detection and reporting, identifying weak points in your security framework. This feature enables organizations to address critical vulnerabilities quickly, reducing the likelihood of exploitation by cybercriminals.
Use Cases of Threat Watch
Protecting Employee Credentials
Organizations can leverage Threat Watch to protect employee credentials by continuously monitoring for breaches and compromised accounts. This use case ensures that sensitive information remains secure and minimizes the risk of unauthorized access.
Identifying Phishing Threats
Threat Watch helps security teams identify and mitigate phishing threats in real-time. By analyzing suspicious addresses and links, organizations can prevent potential data breaches and protect their employees from social engineering attacks.
Improving Incident Response Times
With its automated insights, Threat Watch enhances incident response times. Security teams can quickly prioritize and address critical vulnerabilities, ensuring that threats are contained before they can escalate into significant security incidents.
Comprehensive Security Health Evaluation
Organizations can use Threat Watch for a comprehensive evaluation of their cybersecurity health. Regular scans assess critical security categories, providing actionable insights that help strengthen overall security posture and compliance.
Frequently Asked Questions
What types of threats does Threat Watch monitor?
Threat Watch monitors a wide range of threats, including compromised credentials, phishing addresses, breached accounts, and vulnerabilities across the surface, deep, and dark web.
How quickly can Threat Watch identify risks?
Threat Watch is designed for speed, providing real-time risk assessments that allow organizations to identify critical threats as they emerge, ensuring timely action.
Is there a trial available for Threat Watch?
Yes, Threat Watch offers a free initial scan, allowing organizations to evaluate its capabilities and understand their cybersecurity posture before making a commitment.
Can Threat Watch integrate with existing security tools?
Threat Watch is designed to complement existing security tools and frameworks, making it easier for organizations to enhance their cybersecurity strategies without overhauling their current systems.
Explore more in this category:
Similar to Threat Watch
Generate unique, catchy business names in seconds with our lightning-fast free AI generator designed for startups and brands.
ROIpad delivers data-backed insights to refine your B2B SaaS positioning and accelerate your go-to-market strategy for maximum impact.
MarketWrk automates pricing and MAP monitoring to instantly protect your brand and margins.
Opal44 delivers AI-powered website traffic insights in plain English, making analytics easy and actionable for everyone.
Fusedash transforms raw data into interactive dashboards and charts, enabling instant insights for your team.
finban simplifies liquidity planning, empowering confident decisions on hiring, taxes, and investments without Excel.
Zignt creates and sends unlimited legally binding contracts instantly with zero per-signature fees and bank-level.
aVenture delivers rapid insights on startups, funding, and investors, empowering you to seize emerging opportunities.
