Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right product.
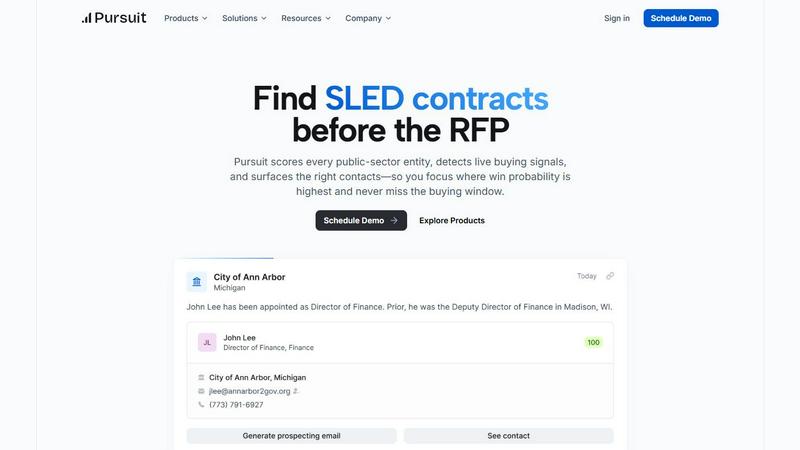
Pursuit
Pursuit delivers early buying signals and actionable insights for winning public sector deals before RFPs are issued.
Last updated: February 28, 2026
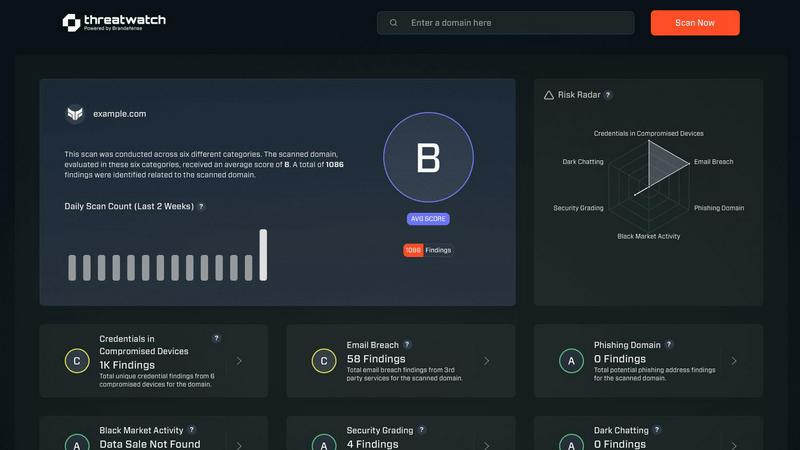
Threat Watch
Rapidly assess your cybersecurity health with Threat Watch for instant insights on compromised accounts and devices.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Real-Time Buying Signals
Pursuit identifies buying signals well in advance, allowing teams to prepare and position themselves strategically before RFPs are issued. This foresight is critical for maintaining a competitive edge.
Comprehensive Database
With access to a vast database of over 110,000 public-sector entities, Pursuit provides users with the insights they need to navigate various procurement processes and budget cycles efficiently.
Seamless Integration
Pursuit integrates natively with major CRM platforms like Salesforce and HubSpot, ensuring that data flows effortlessly throughout your organization without the need for engineering resources.
Configurable Alerts
Users can set up customizable alerts for contract renewals, budget approvals, and leadership changes, enabling proactive engagement with potential clients and reducing churn risk.
Threat Watch
Real-time Risk Assessment
Threat Watch delivers real-time risk assessments by continuously monitoring your organization’s digital footprint. This feature ensures that you are always aware of your current security posture, allowing for quick responses to emerging threats.
Comprehensive Threat Intelligence
With comprehensive threat intelligence, Threat Watch aggregates data from the surface, deep, and dark web. This feature enables users to gain insights into potential vulnerabilities and threats, transforming raw data into meaningful action plans.
Automated Credential Monitoring
Automated credential monitoring scans for compromised employee credentials and breached accounts, alerting your security team instantly. This proactive feature helps mitigate risks associated with unauthorized access and data breaches.
Vulnerability Detection and Reporting
Threat Watch provides robust vulnerability detection and reporting, identifying weak points in your security framework. This feature enables organizations to address critical vulnerabilities quickly, reducing the likelihood of exploitation by cybercriminals.
Use Cases
Pursuit
Sales Team Optimization
Sales representatives can utilize Pursuit to receive prioritized call lists based on real-time buying signals, significantly increasing the chances of engaging with qualified leads.
Marketing Campaigns
Marketing teams can build targeted Account-Based Marketing (ABM) campaigns around actionable insights from Pursuit, leading to higher conversion rates and more effective audience engagement.
Revenue Operations
Revenue operations teams benefit from Pursuit's high data accuracy and continuous enrichment, allowing for better forecasting and strategic decision-making without excessive overhead.
Customer Success Management
Customer success teams can monitor contract renewal timelines and churn signals, providing them with the tools necessary to identify risks and opportunities for upselling or renewal well in advance.
Threat Watch
Protecting Employee Credentials
Organizations can leverage Threat Watch to protect employee credentials by continuously monitoring for breaches and compromised accounts. This use case ensures that sensitive information remains secure and minimizes the risk of unauthorized access.
Identifying Phishing Threats
Threat Watch helps security teams identify and mitigate phishing threats in real-time. By analyzing suspicious addresses and links, organizations can prevent potential data breaches and protect their employees from social engineering attacks.
Improving Incident Response Times
With its automated insights, Threat Watch enhances incident response times. Security teams can quickly prioritize and address critical vulnerabilities, ensuring that threats are contained before they can escalate into significant security incidents.
Comprehensive Security Health Evaluation
Organizations can use Threat Watch for a comprehensive evaluation of their cybersecurity health. Regular scans assess critical security categories, providing actionable insights that help strengthen overall security posture and compliance.
Overview
About Pursuit
Pursuit is an advanced AI-driven platform specifically designed to revolutionize the selling process to the public sector. By leveraging real-time data, Pursuit scores every public-sector entity and surfaces vital buying signals 6-18 months before Requests for Proposals (RFPs) go live. This proactive approach enables businesses to position themselves as incumbents rather than outsiders when opportunities arise. Tailored for organizations aiming to enhance their efficiency in navigating complex public sector contracts, Pursuit ensures users never miss critical buying windows. With a robust database of over 110,000 public sector entities and continuous data enrichment, Pursuit empowers sales teams to focus on high-probability opportunities, effectively reducing time spent on research and increasing conversion rates. By streamlining the sales process and facilitating connections with key decision-makers, Pursuit transforms how organizations engage with the public sector, making it easier than ever to drive growth and success.
About Threat Watch
Threat Watch is your organization’s lightning-fast command center for cybersecurity intelligence, designed to provide an immediate, crystal-clear view of your digital security posture. This unified platform continuously analyzes your assets, vulnerabilities, and exposures across the surface, deep, and dark web. By transforming complex threat data into actionable insights, Threat Watch empowers IT leaders, security teams, and business executives to move at the speed of risk. Its core value proposition lies in speed and efficiency, enabling users to identify critical risks in real-time and prioritize them based on actual business impact. With Threat Watch, organizations can execute mitigation strategies faster than threats can evolve, automating the heavy lifting of cyber threat intelligence. From detecting compromised employee credentials and breached accounts to identifying phishing addresses and vulnerable devices, Threat Watch saves you the most valuable resource—time—ensuring your cybersecurity health is always a priority.
Frequently Asked Questions
Pursuit FAQ
How does Pursuit help my sales team?
Pursuit helps sales teams by providing real-time buying signals and prioritized call lists, enabling them to engage with qualified leads more effectively and efficiently.
What types of organizations can benefit from using Pursuit?
Any organization aiming to sell to the public sector can benefit from Pursuit, particularly those targeting state and local government entities within the SLED market.
How accurate is the data provided by Pursuit?
Pursuit boasts a 94% accuracy rate in its data, thanks to continuous enrichment processes that ensure users have access to the most current and relevant information.
Can Pursuit integrate with my existing CRM?
Yes, Pursuit offers seamless integration with popular CRM platforms like Salesforce and HubSpot, ensuring smooth data flow and operational efficiency without additional engineering work.
Threat Watch FAQ
What types of threats does Threat Watch monitor?
Threat Watch monitors a wide range of threats, including compromised credentials, phishing addresses, breached accounts, and vulnerabilities across the surface, deep, and dark web.
How quickly can Threat Watch identify risks?
Threat Watch is designed for speed, providing real-time risk assessments that allow organizations to identify critical threats as they emerge, ensuring timely action.
Is there a trial available for Threat Watch?
Yes, Threat Watch offers a free initial scan, allowing organizations to evaluate its capabilities and understand their cybersecurity posture before making a commitment.
Can Threat Watch integrate with existing security tools?
Threat Watch is designed to complement existing security tools and frameworks, making it easier for organizations to enhance their cybersecurity strategies without overhauling their current systems.
Alternatives
Pursuit Alternatives
Pursuit is an innovative AI-driven tool that streamlines revenue generation in the public sector, providing actionable insights and live buying signals. It falls under the Business Intelligence category, specifically designed for organizations aiming to enhance their efficiency in securing public sector contracts. Users often seek alternatives due to various reasons, including pricing, feature sets, or specific platform requirements that may better suit their business needs. When exploring alternatives, consider aspects such as the comprehensiveness of the data provided, ease of integration with existing systems, and the ability to deliver real-time alerts and insights. Assessing user support and overall user experience can also be critical in finding a solution that aligns with your sales strategy and objectives.
Threat Watch Alternatives
Threat Watch is a powerful cybersecurity intelligence platform that helps organizations instantly assess and monitor their cybersecurity health. It falls under the category of business intelligence, specifically tailored for IT leaders and security teams who need to act quickly on potential threats. Users often seek alternatives to Threat Watch due to various factors, including pricing, specific feature sets, or integration capabilities with existing platforms. When searching for an alternative, it's crucial to consider aspects like real-time monitoring capabilities, ease of use, and the ability to prioritize risk based on business impact. --- [{"question": "What is Threat Watch?", "answer": "Threat Watch is a cybersecurity intelligence platform that provides instant evaluations of an organization's cybersecurity health, delivering actionable insights to enhance security posture."},{"question": "Who is Threat Watch for?", "answer": "Threat Watch is designed for IT leaders, security teams, and business executives who require fast and efficient cybersecurity intelligence to mitigate risks."},{"question": "Is Threat Watch free?", "answer": "Threat Watch is a subscription-based service, and pricing details can vary based on the specific needs of the organization."},{"question": "What are the main features of Threat Watch?", "answer": "Main features of Threat Watch include a real-time cyber health dashboard, automated exposure scanning, and prioritized risk intelligence for effective threat management."}]
