iGPT vs Threat Watch
Side-by-side comparison to help you choose the right product.
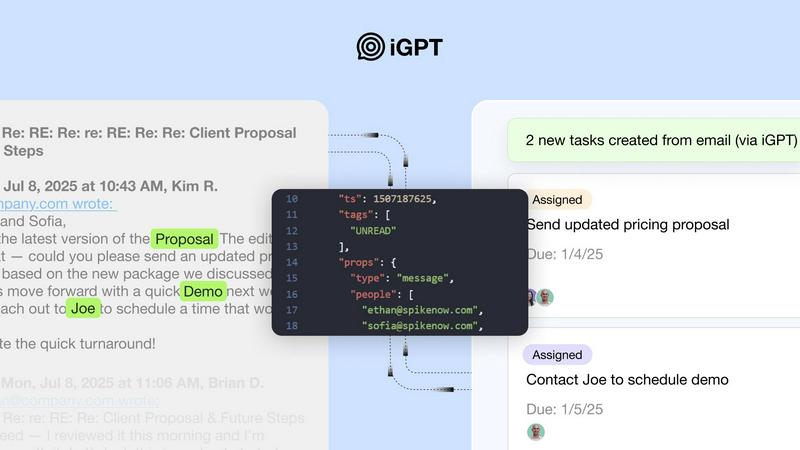
iGPT instantly turns messy email data into trusted, actionable insights for enterprise agents.
Last updated: February 28, 2026
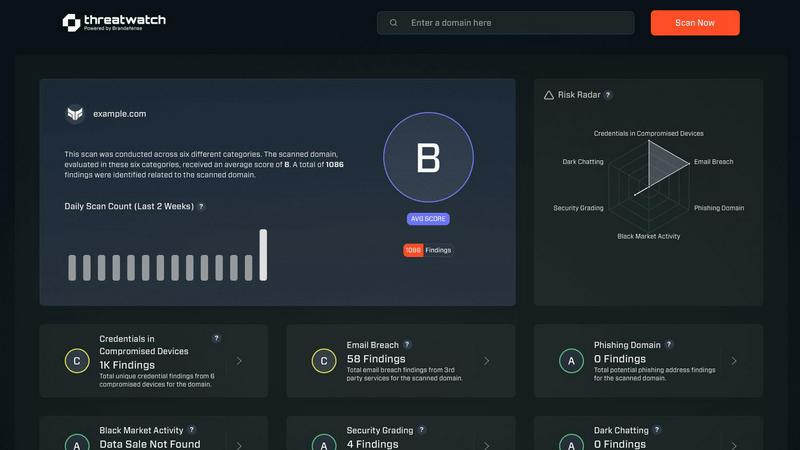
Threat Watch
Rapidly assess your cybersecurity health with Threat Watch for instant insights on compromised accounts and devices.
Last updated: March 1, 2026
Visual Comparison
iGPT
Threat Watch
Feature Comparison
iGPT
Unified Intelligence Endpoint
Replace complex multi-step pipelines with one simple API call. iGPT's single endpoint handles retrieval, context shaping, and reasoning in a unified, blazing-fast pipeline. You provide a natural language query, and it returns a structured, cited answer—bypassing the need for separate vector stores, parsing logic, and fragile prompt chains. This streamlined approach slashes development time and operational overhead.
Real-Time Ingestion & Thread Reconstruction
iGPT indexes new messages and attachments instantly, ensuring your AI agents always operate on the latest data. It doesn't just read individual emails; it automatically reconstructs full conversation threads across time, participants, and attachments. This provides agents with the complete narrative context, crucial for understanding nuanced discussions, decisions, and action items.
Advanced Attachment Processing
Go beyond email body text. iGPT deeply processes attachments—including documents, PDFs, and spreadsheets—extracting text, data, and structure. This intelligence is seamlessly integrated with the email thread context, allowing queries to surface insights from contracts in an update or figures from a report, all within the conversational flow.
Enterprise-Grade Security & Audit
Built with zero data training, zero data retention, and strict OAuth-only Role-Based Access Control (RBAC). Every inference is processed in memory and never stored, ensuring your sensitive communications never leak. Full audit trails make every response traceable back to its source, providing the compliance and trust required for enterprise deployment.
Threat Watch
Real-time Risk Assessment
Threat Watch delivers real-time risk assessments by continuously monitoring your organization’s digital footprint. This feature ensures that you are always aware of your current security posture, allowing for quick responses to emerging threats.
Comprehensive Threat Intelligence
With comprehensive threat intelligence, Threat Watch aggregates data from the surface, deep, and dark web. This feature enables users to gain insights into potential vulnerabilities and threats, transforming raw data into meaningful action plans.
Automated Credential Monitoring
Automated credential monitoring scans for compromised employee credentials and breached accounts, alerting your security team instantly. This proactive feature helps mitigate risks associated with unauthorized access and data breaches.
Vulnerability Detection and Reporting
Threat Watch provides robust vulnerability detection and reporting, identifying weak points in your security framework. This feature enables organizations to address critical vulnerabilities quickly, reducing the likelihood of exploitation by cybercriminals.
Use Cases
iGPT
Intelligent Email Assistants
Build AI copilots that draft, prioritize, summarize, and act on email with full historical and attachment context. Agents can understand project status from long threads, identify urgent requests, and generate informed replies without requiring a human to manually piece together the story.
Automated Workflow Orchestration
Turn email threads into automated tasks, deadlines, and approval processes directly in your project management or CRM tools. iGPT can extract action items, owners, and dates from messy discussions and flag stalled items, streamlining operational workflows and ensuring follow-through.
Customer Support Copilots
Empower support teams by instantly rebuilding the complete customer journey. iGPT pulls together every email, attachment, and tone shift across long chains, giving agents immediate context to resolve issues faster and provide personalized, informed service without manual digging.
Compliance & CRM Intelligence
Automatically trace feedback, approvals, and deal rationale back to the original email and attachment sources for robust audit trails. For sales teams, extract key decisions, stakeholder sentiment, and deal momentum directly from email threads to keep CRM data accurate and actionable.
Threat Watch
Protecting Employee Credentials
Organizations can leverage Threat Watch to protect employee credentials by continuously monitoring for breaches and compromised accounts. This use case ensures that sensitive information remains secure and minimizes the risk of unauthorized access.
Identifying Phishing Threats
Threat Watch helps security teams identify and mitigate phishing threats in real-time. By analyzing suspicious addresses and links, organizations can prevent potential data breaches and protect their employees from social engineering attacks.
Improving Incident Response Times
With its automated insights, Threat Watch enhances incident response times. Security teams can quickly prioritize and address critical vulnerabilities, ensuring that threats are contained before they can escalate into significant security incidents.
Comprehensive Security Health Evaluation
Organizations can use Threat Watch for a comprehensive evaluation of their cybersecurity health. Regular scans assess critical security categories, providing actionable insights that help strengthen overall security posture and compliance.
Overview
About iGPT
iGPT is the lightning-fast email intelligence API engineered for the enterprise. It solves the critical problem where most AI fails: unlocking the immense, unstructured value trapped within email conversations and attachments. Built for developers and organizations deploying agentic workflows, iGPT provides a single, unified endpoint to instantly access, understand, and act upon your entire email corpus. It eliminates the traditional AI development grind—no manual parsing, chunking, indexing, or endless prompt tuning. Instead, you send a simple natural language request and get a structured, context-aware answer with full citations in seconds. With its cutting-edge Context Engineering Framework (CEF), iGPT delivers end-to-end security, granular RBAC controls, and comprehensive audit trails. This allows teams to build powerful email assistants, automate complex workflows, and extract actionable insights with unparalleled speed and trust, transforming email from a communication tool into a core intelligence asset.
About Threat Watch
Threat Watch is your organization’s lightning-fast command center for cybersecurity intelligence, designed to provide an immediate, crystal-clear view of your digital security posture. This unified platform continuously analyzes your assets, vulnerabilities, and exposures across the surface, deep, and dark web. By transforming complex threat data into actionable insights, Threat Watch empowers IT leaders, security teams, and business executives to move at the speed of risk. Its core value proposition lies in speed and efficiency, enabling users to identify critical risks in real-time and prioritize them based on actual business impact. With Threat Watch, organizations can execute mitigation strategies faster than threats can evolve, automating the heavy lifting of cyber threat intelligence. From detecting compromised employee credentials and breached accounts to identifying phishing addresses and vulnerable devices, Threat Watch saves you the most valuable resource—time—ensuring your cybersecurity health is always a priority.
Frequently Asked Questions
iGPT FAQ
How does iGPT handle data privacy and security?
iGPT is architected for maximum enterprise security. It operates on a zero-data training and zero-data retention policy—your data is never used to train models or stored after processing. All access is governed by OAuth with strict Role-Based Access Control (RBAC), and every API call provides a full, citable audit trail.
What is the typical response time for a query?
Performance is a core design principle. iGPT delivers retrieval in approximately 200 milliseconds and generates the first token of a response in about 3 seconds, even when querying across large, complex datasets of emails and attachments. This speed enables real-time agent interactions.
Do I need to manage vector databases or chunking logic?
No. iGPT is a fully managed API that eliminates the infrastructure complexity. There is no need for you to parse emails, chunk text, maintain vector indexes, or tune retrieval prompts. You connect your data sources, and iGPT handles the entire context engineering pipeline automatically.
What kinds of data sources can iGPT connect to?
iGPT is built primarily for enterprise email systems (like Google Workspace and Microsoft 365) and their associated attachment data. It deeply indexes this information, providing a unified intelligence layer over your organization's primary communication channel where critical work happens.
Threat Watch FAQ
What types of threats does Threat Watch monitor?
Threat Watch monitors a wide range of threats, including compromised credentials, phishing addresses, breached accounts, and vulnerabilities across the surface, deep, and dark web.
How quickly can Threat Watch identify risks?
Threat Watch is designed for speed, providing real-time risk assessments that allow organizations to identify critical threats as they emerge, ensuring timely action.
Is there a trial available for Threat Watch?
Yes, Threat Watch offers a free initial scan, allowing organizations to evaluate its capabilities and understand their cybersecurity posture before making a commitment.
Can Threat Watch integrate with existing security tools?
Threat Watch is designed to complement existing security tools and frameworks, making it easier for organizations to enhance their cybersecurity strategies without overhauling their current systems.
Alternatives
iGPT Alternatives
iGPT is a powerful Business Intelligence API that transforms enterprise email data into secure, context-aware insights. It acts as a secure gateway, turning complex email conversations and attachments into trusted intelligence for agentic workflows and smarter decision-making. Users often explore alternatives for various reasons. Needs around specific pricing models, unique feature requirements, or different platform integration capabilities can drive the search. Some organizations may require a solution tailored to a particular niche or a different balance of automation versus control. When evaluating options, prioritize core capabilities. Look for robust security and compliance features, real-time data processing, and the ability to deliver actionable, cited insights. The ideal solution should integrate swiftly, provide full auditability, and scale efficiently with your enterprise's operational tempo.
Threat Watch Alternatives
Threat Watch is a powerful cybersecurity intelligence platform that helps organizations instantly assess and monitor their cybersecurity health. It falls under the category of business intelligence, specifically tailored for IT leaders and security teams who need to act quickly on potential threats. Users often seek alternatives to Threat Watch due to various factors, including pricing, specific feature sets, or integration capabilities with existing platforms. When searching for an alternative, it's crucial to consider aspects like real-time monitoring capabilities, ease of use, and the ability to prioritize risk based on business impact. --- [{"question": "What is Threat Watch?", "answer": "Threat Watch is a cybersecurity intelligence platform that provides instant evaluations of an organization's cybersecurity health, delivering actionable insights to enhance security posture."},{"question": "Who is Threat Watch for?", "answer": "Threat Watch is designed for IT leaders, security teams, and business executives who require fast and efficient cybersecurity intelligence to mitigate risks."},{"question": "Is Threat Watch free?", "answer": "Threat Watch is a subscription-based service, and pricing details can vary based on the specific needs of the organization."},{"question": "What are the main features of Threat Watch?", "answer": "Main features of Threat Watch include a real-time cyber health dashboard, automated exposure scanning, and prioritized risk intelligence for effective threat management."}]
