Deeploy vs Threat Watch
Side-by-side comparison to help you choose the right product.

Deeploy
Deeploy empowers organizations to manage AI governance, ensuring compliance, reducing risk, and enabling scalable.
Last updated: March 1, 2026
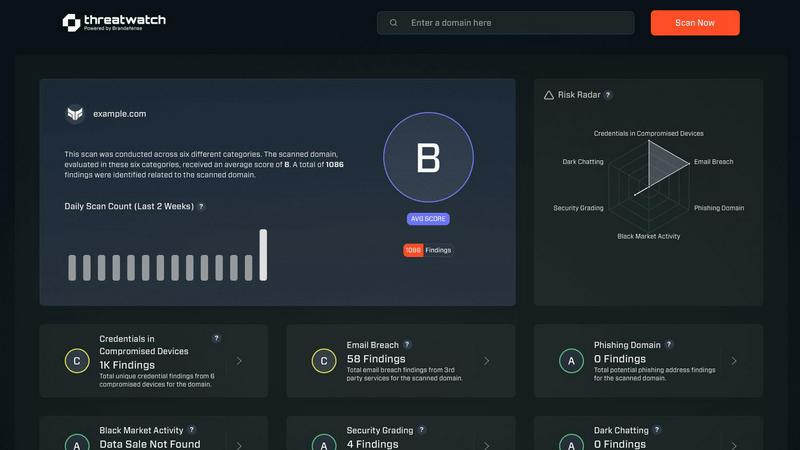
Threat Watch
Rapidly assess your cybersecurity health with Threat Watch for instant insights on compromised accounts and devices.
Last updated: March 1, 2026
Visual Comparison
Deeploy
Threat Watch
Feature Comparison
Deeploy
AI Discovery and Onboarding
Deeploy offers complete visibility across your AI landscape, allowing organizations to discover, onboard, and manage all AI systems from a single interface. This feature connects seamlessly with any MLOps or GenAI platform, eliminating blind spots and achieving centralized control without the pains of migration.
Control Frameworks
With Deeploy, organizations can navigate AI regulations confidently using guided workflows for straightforward compliance. Users can choose from default control frameworks like ISO 42001 or NIST AI RMF, or build custom frameworks, ensuring that classifying AI system risks is quick and efficient while establishing accountability.
Control Implementation
Deeploy turns governance frameworks into enforceable controls that engineers can easily follow. This feature accelerates compliance by up to 90% using templates and automatically collected evidence, ensuring that engineers receive clear, actionable requirements for each AI system.
Real-Time Monitoring
The real-time monitoring feature prevents AI incidents before they occur, offering instant alerts for model drift or performance drops. It ensures organizations can identify errors and anomalies proactively, maintaining oversight and compliance across all AI systems in production while adding tracing and guardrails for enhanced protection.
Threat Watch
Real-time Risk Assessment
Threat Watch delivers real-time risk assessments by continuously monitoring your organization’s digital footprint. This feature ensures that you are always aware of your current security posture, allowing for quick responses to emerging threats.
Comprehensive Threat Intelligence
With comprehensive threat intelligence, Threat Watch aggregates data from the surface, deep, and dark web. This feature enables users to gain insights into potential vulnerabilities and threats, transforming raw data into meaningful action plans.
Automated Credential Monitoring
Automated credential monitoring scans for compromised employee credentials and breached accounts, alerting your security team instantly. This proactive feature helps mitigate risks associated with unauthorized access and data breaches.
Vulnerability Detection and Reporting
Threat Watch provides robust vulnerability detection and reporting, identifying weak points in your security framework. This feature enables organizations to address critical vulnerabilities quickly, reducing the likelihood of exploitation by cybercriminals.
Use Cases
Deeploy
Streamlined Compliance Management
Organizations can utilize Deeploy to simplify compliance management across various AI initiatives, ensuring adherence to regulations like the EU AI Act. The software facilitates efficient oversight and reduces the risk of non-compliance.
Enhanced AI System Visibility
Deeploy empowers businesses to gain complete visibility over their AI systems, allowing stakeholders to track model performance and compliance in real-time. This visibility is critical for effective decision-making and risk management.
Accelerated Model Deployment
With Deeploy, the process of deploying AI models is dramatically streamlined, reducing deployment times from days to mere hours. This acceleration enables teams to iterate quickly, fostering innovation and responsiveness to market needs.
Improved Human Oversight
Deeploy establishes effective human oversight of AI systems, allowing organizations to leverage expert feedback loops and monitoring capabilities. This ensures responsible AI usage and enhances the quality of AI-driven outcomes across various applications.
Threat Watch
Protecting Employee Credentials
Organizations can leverage Threat Watch to protect employee credentials by continuously monitoring for breaches and compromised accounts. This use case ensures that sensitive information remains secure and minimizes the risk of unauthorized access.
Identifying Phishing Threats
Threat Watch helps security teams identify and mitigate phishing threats in real-time. By analyzing suspicious addresses and links, organizations can prevent potential data breaches and protect their employees from social engineering attacks.
Improving Incident Response Times
With its automated insights, Threat Watch enhances incident response times. Security teams can quickly prioritize and address critical vulnerabilities, ensuring that threats are contained before they can escalate into significant security incidents.
Comprehensive Security Health Evaluation
Organizations can use Threat Watch for a comprehensive evaluation of their cybersecurity health. Regular scans assess critical security categories, providing actionable insights that help strengthen overall security posture and compliance.
Overview
About Deeploy
Deeploy is a cutting-edge AI governance software tailored for organizations that heavily depend on AI technologies. It centralizes oversight, compliance, and monitoring of AI systems, enabling businesses to navigate the complex landscape of AI regulations, including the EU AI Act. With Deeploy, companies gain complete visibility into their AI models, regardless of their origin or deployment stage. It simplifies onboarding, integrating various MLOps and GenAI platforms seamlessly, eliminating the headaches typically associated with migration. Real-time explainability, human feedback loops, and comprehensive audit trails empower organizations to mitigate risks associated with AI deployment while fostering trust and transparency. Deeploy is the solution for businesses looking for an efficient, streamlined governance approach that enhances operational efficiency and ensures compliance across all AI initiatives.
About Threat Watch
Threat Watch is your organization’s lightning-fast command center for cybersecurity intelligence, designed to provide an immediate, crystal-clear view of your digital security posture. This unified platform continuously analyzes your assets, vulnerabilities, and exposures across the surface, deep, and dark web. By transforming complex threat data into actionable insights, Threat Watch empowers IT leaders, security teams, and business executives to move at the speed of risk. Its core value proposition lies in speed and efficiency, enabling users to identify critical risks in real-time and prioritize them based on actual business impact. With Threat Watch, organizations can execute mitigation strategies faster than threats can evolve, automating the heavy lifting of cyber threat intelligence. From detecting compromised employee credentials and breached accounts to identifying phishing addresses and vulnerable devices, Threat Watch saves you the most valuable resource—time—ensuring your cybersecurity health is always a priority.
Frequently Asked Questions
Deeploy FAQ
What types of organizations can benefit from Deeploy?
Deeploy is designed for organizations of all sizes that rely on AI technologies, particularly those facing compliance challenges and looking to improve governance and oversight of their AI systems.
How does Deeploy ensure compliance with AI regulations?
Deeploy provides guided workflows for navigating AI regulations, allowing organizations to choose from established control frameworks or create custom ones to meet their specific compliance needs while automating documentation and evidence collection.
Can Deeploy integrate with existing AI tools and platforms?
Yes, Deeploy offers flexible onboarding that allows seamless integration with a variety of MLOps and GenAI platforms, ensuring organizations can centralize their AI governance without the hassle of migration.
What kind of support does Deeploy offer for real-time monitoring?
Deeploy includes robust real-time monitoring capabilities that provide instant alerts for model performance issues and ensure organizations can proactively identify and address potential compliance risks before they escalate.
Threat Watch FAQ
What types of threats does Threat Watch monitor?
Threat Watch monitors a wide range of threats, including compromised credentials, phishing addresses, breached accounts, and vulnerabilities across the surface, deep, and dark web.
How quickly can Threat Watch identify risks?
Threat Watch is designed for speed, providing real-time risk assessments that allow organizations to identify critical threats as they emerge, ensuring timely action.
Is there a trial available for Threat Watch?
Yes, Threat Watch offers a free initial scan, allowing organizations to evaluate its capabilities and understand their cybersecurity posture before making a commitment.
Can Threat Watch integrate with existing security tools?
Threat Watch is designed to complement existing security tools and frameworks, making it easier for organizations to enhance their cybersecurity strategies without overhauling their current systems.
Alternatives
Deeploy Alternatives
Deeploy is an advanced AI governance software that centralizes oversight and compliance for AI systems within organizations. It allows businesses to manage their AI landscape effectively, ensuring visibility and adherence to regulations such as the EU AI Act. Users often seek alternatives to Deeploy for reasons like pricing, specific feature requirements, or compatibility with existing platforms. When looking for an alternative, it's essential to consider factors such as ease of integration, scalability, compliance support, and the ability to provide real-time insights and governance. Choosing the right alternative involves evaluating the software's ability to seamlessly onboard existing AI systems and provide robust frameworks for compliance. Users should also look for solutions that prioritize user experience, ensuring that governance processes are intuitive and efficient, with minimal disruption to ongoing operations. Ultimately, the goal is to find a platform that enhances operational efficiency while maintaining rigorous oversight of AI deployments.
Threat Watch Alternatives
Threat Watch is a powerful cybersecurity intelligence platform that helps organizations instantly assess and monitor their cybersecurity health. It falls under the category of business intelligence, specifically tailored for IT leaders and security teams who need to act quickly on potential threats. Users often seek alternatives to Threat Watch due to various factors, including pricing, specific feature sets, or integration capabilities with existing platforms. When searching for an alternative, it's crucial to consider aspects like real-time monitoring capabilities, ease of use, and the ability to prioritize risk based on business impact. --- [{"question": "What is Threat Watch?", "answer": "Threat Watch is a cybersecurity intelligence platform that provides instant evaluations of an organization's cybersecurity health, delivering actionable insights to enhance security posture."},{"question": "Who is Threat Watch for?", "answer": "Threat Watch is designed for IT leaders, security teams, and business executives who require fast and efficient cybersecurity intelligence to mitigate risks."},{"question": "Is Threat Watch free?", "answer": "Threat Watch is a subscription-based service, and pricing details can vary based on the specific needs of the organization."},{"question": "What are the main features of Threat Watch?", "answer": "Main features of Threat Watch include a real-time cyber health dashboard, automated exposure scanning, and prioritized risk intelligence for effective threat management."}]
