CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right product.
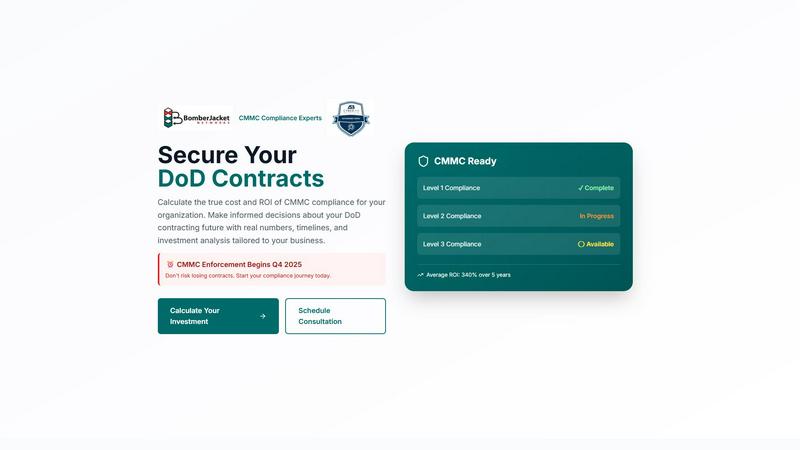
CMMC ROI
CMMC ROI instantly calculates your compliance costs and investment returns for DoD contracts.
Last updated: March 1, 2026
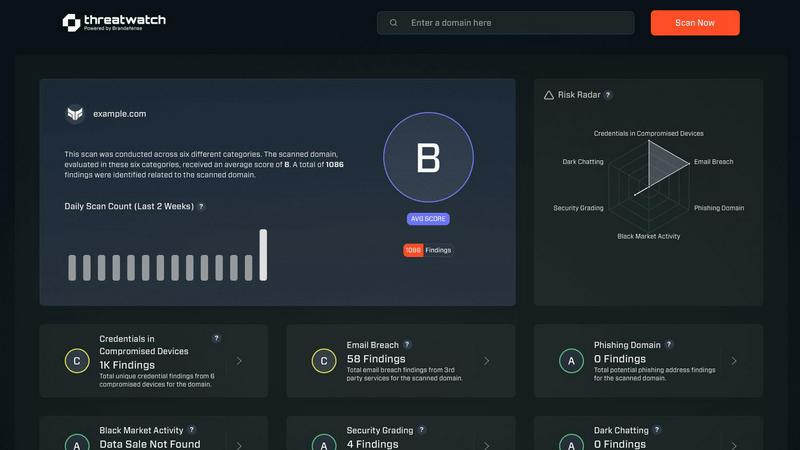
Threat Watch
Rapidly assess your cybersecurity health with Threat Watch for instant insights on compromised accounts and devices.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI
Threat Watch
Feature Comparison
CMMC ROI
Dynamic Investment Calculator
This core feature provides instant, personalized financial modeling. Simply input your company size, DoD revenue, required CMMC level, and current progress to generate a detailed 5-year investment range, ROI percentage, and precise break-even point. It eliminates guesswork with real-time calculations.
Scenario-Based Quick Examples
Jumpstart your planning with pre-loaded scenarios for common contractor profiles, from small FCI handlers to large prime contractors. Each example displays immediate investment estimates, allowing for rapid benchmarking and understanding of potential cost ranges before entering your specific data.
Detailed ROI Timeline Projection
Visualize your entire compliance journey on an interactive 5-year timeline chart. This feature clearly plots cumulative expenditures against protected contract value, highlighting the exact month you break even and how your investment grows into significant returns over time.
Critical Risk Assessment Dashboard
Instantly see the stakes of non-compliance. The dashboard quantifies your contract value at risk, estimates the average cost of a breach or false claims penalty avoided, and shows the competitive win-rate advantage gained with CMMC certification, framing compliance as essential risk management.
Threat Watch
Real-time Risk Assessment
Threat Watch delivers real-time risk assessments by continuously monitoring your organization’s digital footprint. This feature ensures that you are always aware of your current security posture, allowing for quick responses to emerging threats.
Comprehensive Threat Intelligence
With comprehensive threat intelligence, Threat Watch aggregates data from the surface, deep, and dark web. This feature enables users to gain insights into potential vulnerabilities and threats, transforming raw data into meaningful action plans.
Automated Credential Monitoring
Automated credential monitoring scans for compromised employee credentials and breached accounts, alerting your security team instantly. This proactive feature helps mitigate risks associated with unauthorized access and data breaches.
Vulnerability Detection and Reporting
Threat Watch provides robust vulnerability detection and reporting, identifying weak points in your security framework. This feature enables organizations to address critical vulnerabilities quickly, reducing the likelihood of exploitation by cybercriminals.
Use Cases
CMMC ROI
Securing New DoD Contract Bids
A mid-sized technology firm bidding on a Level 2 contract uses the calculator to model the required compliance investment against the potential $15M contract value. The clear ROI projection strengthens their proposal and justifies the upfront security spend to leadership and investors.
Justifying Compliance Budget to Leadership
A CFO at a small contractor needs to approve a significant security budget. They use the tool to generate an executive briefing, showcasing a 212% ROI and an 11-month payback period by protecting $2.5M in annual DoD revenue, turning a security cost into a defensible business investment.
Planning a Multi-Year Compliance Roadmap
A large prime contractor targeting Level 3 certification utilizes the detailed timeline projection to plan resource allocation and capital expenditures over the 12-month implementation journey and subsequent maintenance phases, ensuring smooth, budgeted progression toward certification.
Assessing Competitive Market Position
A business development manager evaluates their firm's position against uncertified competitors. The risk assessment dashboard confirms a 100% win-rate advantage with certification, providing a data-backed argument to accelerate their CMMC program to capture market share before enforcement.
Threat Watch
Protecting Employee Credentials
Organizations can leverage Threat Watch to protect employee credentials by continuously monitoring for breaches and compromised accounts. This use case ensures that sensitive information remains secure and minimizes the risk of unauthorized access.
Identifying Phishing Threats
Threat Watch helps security teams identify and mitigate phishing threats in real-time. By analyzing suspicious addresses and links, organizations can prevent potential data breaches and protect their employees from social engineering attacks.
Improving Incident Response Times
With its automated insights, Threat Watch enhances incident response times. Security teams can quickly prioritize and address critical vulnerabilities, ensuring that threats are contained before they can escalate into significant security incidents.
Comprehensive Security Health Evaluation
Organizations can use Threat Watch for a comprehensive evaluation of their cybersecurity health. Regular scans assess critical security categories, providing actionable insights that help strengthen overall security posture and compliance.
Overview
About CMMC ROI
CMMC ROI is a lightning-fast, data-driven compliance calculator and strategic tool from BomberJacket Networks, an authorized C3PAO and service-disabled veteran-owned business. It is designed exclusively for Department of Defense (DoD) contractors to cut through the uncertainty of Cybersecurity Maturity Model Certification (CMMC). This tool delivers precise, personalized financial projections, calculating the true 5-year cost, return on investment (ROI), and payback period for achieving compliance. It transforms a complex security mandate into a clear business decision, empowering contractors to secure their contracting future with confidence. With CMMC enforcement beginning in Q4 2025, this tool provides the speed and clarity needed to act decisively, protect existing contract revenue, and gain a competitive edge. It translates over 20 years of federal cybersecurity expertise into actionable intelligence, helping you minimize risk and maximize your investment by providing real numbers and timelines tailored to your unique business size, revenue, and target certification level.
About Threat Watch
Threat Watch is your organization’s lightning-fast command center for cybersecurity intelligence, designed to provide an immediate, crystal-clear view of your digital security posture. This unified platform continuously analyzes your assets, vulnerabilities, and exposures across the surface, deep, and dark web. By transforming complex threat data into actionable insights, Threat Watch empowers IT leaders, security teams, and business executives to move at the speed of risk. Its core value proposition lies in speed and efficiency, enabling users to identify critical risks in real-time and prioritize them based on actual business impact. With Threat Watch, organizations can execute mitigation strategies faster than threats can evolve, automating the heavy lifting of cyber threat intelligence. From detecting compromised employee credentials and breached accounts to identifying phishing addresses and vulnerable devices, Threat Watch saves you the most valuable resource—time—ensuring your cybersecurity health is always a priority.
Frequently Asked Questions
CMMC ROI FAQ
What is the average ROI for CMMC compliance?
Based on typical scenarios, contractors can see an average ROI of 340% over a 5-year period. Your specific ROI is calculated by the tool using your DoD contract revenue, estimated breach cost avoidance ($2.5M), and your total projected implementation, maintenance, and recertification costs.
How accurate are the cost estimates provided?
The estimates are derived from BomberJacket Networks' extensive experience as a C3PAO, with real-world data from hundreds of assessments. Ranges account for variables like company complexity and current security posture, providing a reliable financial model for strategic planning.
What if my company has already started some compliance work?
The calculator includes "Progress Discounts" for this. If you select "In Progress," you receive a 30% reduction on implementation costs; "Nearly Complete" grants a 60% discount. This ensures your ROI calculation reflects your actual starting point, not a generic one.
When do I need to be certified by?
CMMC enforcement begins in Q4 2025. Achieving certification is a process that can take approximately 12 months for Level 2. Starting your journey now is critical to avoid losing contract opportunities and revenue when the rule takes effect.
Threat Watch FAQ
What types of threats does Threat Watch monitor?
Threat Watch monitors a wide range of threats, including compromised credentials, phishing addresses, breached accounts, and vulnerabilities across the surface, deep, and dark web.
How quickly can Threat Watch identify risks?
Threat Watch is designed for speed, providing real-time risk assessments that allow organizations to identify critical threats as they emerge, ensuring timely action.
Is there a trial available for Threat Watch?
Yes, Threat Watch offers a free initial scan, allowing organizations to evaluate its capabilities and understand their cybersecurity posture before making a commitment.
Can Threat Watch integrate with existing security tools?
Threat Watch is designed to complement existing security tools and frameworks, making it easier for organizations to enhance their cybersecurity strategies without overhauling their current systems.
Alternatives
CMMC ROI Alternatives
CMMC ROI is a business intelligence tool designed for DoD contractors. It calculates the precise costs and return on investment for achieving Cybersecurity Maturity Model Certification. This helps organizations make data-driven decisions about their compliance journey. Users often seek alternatives for various reasons. These can include budget constraints, the need for different feature sets like integrated GRC platforms, or a preference for a different service model. The specific needs of a business can drive the search for a different solution. When evaluating other options, focus on core criteria. Look for proven CMMC expertise, transparent pricing models, and a clear path to certification. The right solution should offer a strategic, ROI-focused approach tailored to your contract goals and security posture.
Threat Watch Alternatives
Threat Watch is a powerful cybersecurity intelligence platform that helps organizations instantly assess and monitor their cybersecurity health. It falls under the category of business intelligence, specifically tailored for IT leaders and security teams who need to act quickly on potential threats. Users often seek alternatives to Threat Watch due to various factors, including pricing, specific feature sets, or integration capabilities with existing platforms. When searching for an alternative, it's crucial to consider aspects like real-time monitoring capabilities, ease of use, and the ability to prioritize risk based on business impact. --- [{"question": "What is Threat Watch?", "answer": "Threat Watch is a cybersecurity intelligence platform that provides instant evaluations of an organization's cybersecurity health, delivering actionable insights to enhance security posture."},{"question": "Who is Threat Watch for?", "answer": "Threat Watch is designed for IT leaders, security teams, and business executives who require fast and efficient cybersecurity intelligence to mitigate risks."},{"question": "Is Threat Watch free?", "answer": "Threat Watch is a subscription-based service, and pricing details can vary based on the specific needs of the organization."},{"question": "What are the main features of Threat Watch?", "answer": "Main features of Threat Watch include a real-time cyber health dashboard, automated exposure scanning, and prioritized risk intelligence for effective threat management."}]
