Hush Touch | Voice-to-Text for MacOS vs RedVeil
Side-by-side comparison to help you choose the right product.
Hush Touch | Voice-to-Text for MacOS
Hush Touch is an offline voice-to-text app for Mac that learns your vocabulary and delivers accurate, real-time.
Last updated: February 27, 2026
RedVeil
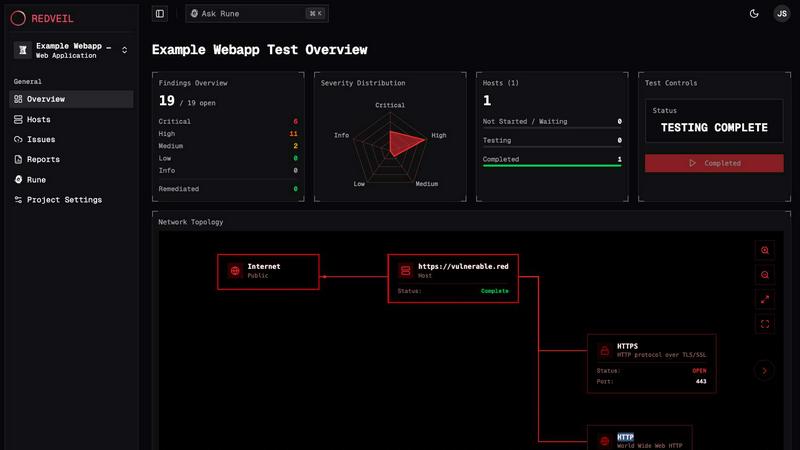
RedVeil delivers rapid, AI-powered penetration testing to uncover vulnerabilities and provide actionable insights.
Last updated: February 27, 2026
Visual Comparison
Hush Touch | Voice-to-Text for MacOS

RedVeil
Feature Comparison
Hush Touch | Voice-to-Text for MacOS
Dual-Engine Recognition
Hush Touch employs a dual-engine system that combines the capabilities of DictationTranscriber for fluid natural language processing and SFSpeechRecognizer for boosting your custom vocabulary. This innovative blend allows for accurate dictation that captures your unique speech patterns and terminology.
Custom Vocabulary
The app supports a custom vocabulary of up to 500 terms, which can learn and adapt based on your corrections. This means whether you are dealing with technical jargon, brand names, or specialized terms, Hush Touch recognizes and incorporates them seamlessly into your dictation.
Smart Text Processing
Experience advanced text processing features, including the removal of filler words and auto-correction capabilities. Hush Touch's smart algorithms facilitate real-time formatting, such as creating numbered lists and eliminating unnecessary words, enhancing the overall clarity and quality of your transcriptions.
100% On-Device Privacy
With Hush Touch, your data remains secure as everything is processed entirely on your Mac. This commitment to user privacy means zero cloud dependency and no data collection, ensuring that your voice and information stay confidential.
RedVeil
AI-Powered Testing
RedVeil utilizes advanced AI agents that can reason through complex, multi-step attack chains. This allows for the identification of real, exploitable vulnerabilities in your systems with remarkable speed and accuracy, ensuring you receive actionable insights in record time.
One-Click Retesting
After remediation, RedVeil offers a seamless one-click retesting feature. This allows teams to verify vulnerabilities have been addressed without the need for repeated scheduling, making it easier and faster to maintain security standards.
Compliance-Ready Reporting
Generate professional, audit-ready reports with just a click. RedVeil’s reports are tailored to meet various compliance standards, including SOC 2, ISO 27001, and PCI-DSS, ensuring that you are always prepared for audits and assessments.
Flexible Testing Scheduling
RedVeil provides the flexibility to allocate and schedule penetration testing according to your needs. Users can initiate tests on-demand, ensuring that security assessments align perfectly with their development cycles and compliance requirements.
Use Cases
Hush Touch | Voice-to-Text for MacOS
Professional Communication
For busy professionals, Hush Touch streamlines the process of drafting emails and messages. Dictate your thoughts in real time, allowing you to focus on content rather than typing, which enhances productivity and efficiency.
Medical Documentation
Healthcare providers can significantly benefit from Hush Touch by dictating patient notes and medical records accurately. With its ability to learn complex medical terminology, the app ensures that vital information is captured correctly without the hassle of manual entry.
Content Creation
Writers and content creators can utilize Hush Touch to brainstorm ideas and draft articles hands-free. The app's intelligent processing and adaptive learning make it an invaluable tool for anyone looking to enhance their writing workflow.
Code and Technical Documentation
Developers and technical writers will appreciate the app's capability to recognize coding terminology and syntax. Dictating code snippets and technical documentation becomes a breeze, allowing for a more fluid and efficient writing process.
RedVeil
Continuous Security Monitoring
For organizations that frequently deploy updates, RedVeil enables continuous security monitoring. Teams can initiate tests whenever changes are made to the environment, ensuring that new vulnerabilities are identified and addressed promptly.
Compliance Preparation
Businesses preparing for compliance audits can leverage RedVeil’s audit-ready reports to meet regulatory requirements efficiently. Regular testing and detailed reporting streamline the audit process, reducing stress and ensuring adherence to standards.
Incident Response Validation
In the aftermath of a security incident, RedVeil can be employed to validate the effectiveness of incident response measures. By conducting a thorough penetration test, teams can uncover any lingering vulnerabilities and strengthen their defenses against future threats.
Risk Assessment for Development Teams
Development teams can utilize RedVeil during the software development lifecycle to conduct risk assessments before product launches. This proactive approach helps identify and mitigate security risks early, reducing the likelihood of vulnerabilities in production environments.
Overview
About Hush Touch | Voice-to-Text for MacOS
Hush Touch is a cutting-edge voice-to-text application designed specifically for macOS, transforming the dictation experience into a fast, natural, and secure process. Built to operate entirely on-device, Hush Touch ensures offline functionality, making it perfect for users who prioritize privacy and efficiency. By harnessing the power of two advanced Apple transcription engines, combined with an Apple Intelligence final pass, it delivers cleaner and more accurate text outputs. The app is lightweight at just 5.5 MB, launches swiftly, and integrates seamlessly into everyday writing tasks with minimal setup required. Ideal for professionals, creatives, and anyone who needs to draft emails, messages, notes, documents, or any content hands-free, Hush Touch empowers users to dictate naturally. With a simple hotkey or voice activation through Siri, users can start dictation effortlessly and let the app auto-insert text after a brief pause. Hush Touch stands out by eliminating cloud reliance, enabling it to remove filler words, enhance punctuation, and evolve its vocabulary, ensuring that transcription remains private, efficient, and user-friendly.
About RedVeil
RedVeil revolutionizes the landscape of penetration testing by combining the intricate reasoning of human hackers with the lightning-fast capabilities of AI technology. Designed for modern engineering teams that deploy code daily, RedVeil eliminates the lengthy and costly traditional pentesting processes that often take weeks to complete. Instead, it empowers users to initiate a full, autonomous penetration test in just minutes. This means you can receive a comprehensive, actionable, and audit-ready report by the afternoon. RedVeil is ideal for security teams, developers, and compliance officers who need swift and reliable security assessments to protect their digital assets. With RedVeil, you can ensure your applications are secure without the delays associated with conventional testing methods.
Frequently Asked Questions
Hush Touch | Voice-to-Text for MacOS FAQ
How accurate is the transcription with Hush Touch?
Hush Touch offers high accuracy in transcription thanks to its dual-engine recognition system and Apple Intelligence final pass, ensuring that your spoken words are captured as intended.
Can I use Hush Touch offline?
Yes, Hush Touch operates entirely on-device, allowing you to dictate without an internet connection, ensuring both privacy and convenience.
How does the custom vocabulary feature work?
The custom vocabulary feature allows you to input specific terms and phrases that Hush Touch will learn over time. This includes corrections you make during dictation, ensuring that the app adapts to your unique language use.
Is there a trial period available for Hush Touch?
Yes, Hush Touch offers a 7-day free trial with no credit card required, allowing you to experience its features and functionality before making a purchase decision.
RedVeil FAQ
Does RedVeil perform a real penetration test?
Yes, RedVeil conducts genuine penetration tests using advanced AI technology to identify exploitable vulnerabilities and provide actionable remediation steps, mimicking the depth of human testers.
How many penetration tests can I do with my annual subscription?
The number of penetration tests you can perform depends on your chosen subscription tier, with options that allow for various testing frequencies and scopes to meet your specific needs.
Is there a chance that my web application or network could go down during the test?
RedVeil is designed to minimize the risk of disruption during testing. However, it is essential to assess the potential impact based on your specific environment and configurations before initiating a test.
What types of testing do you offer? Is authenticated testing supported?
RedVeil offers various testing types, including external web and network testing. Authenticated testing is also supported to provide a comprehensive assessment of your security posture from multiple angles.
Alternatives
Hush Touch | Voice-to-Text for MacOS Alternatives
Hush Touch | Voice-to-Text for MacOS is an innovative tool designed for seamless dictation, fitting into the AI Assistants category. This offline voice-to-text application stands out due to its reliance on on-device processing, ensuring privacy and quick access to transcription. Users often seek alternatives to Hush Touch for various reasons, including pricing, specific feature requirements, or compatibility with different platforms. When looking for alternatives, it’s crucial to consider factors such as ease of use, the accuracy of transcription, offline functionality, and overall cost-effectiveness. Evaluating user reviews and testing out features can also help identify an option that best suits individual dictation needs and enhances productivity.
RedVeil Alternatives
RedVeil is an innovative solution in the realm of penetration testing, harnessing the power of agentic AI to provide on-demand services that reveal vulnerabilities in software systems. As traditional pentesting methods often lag behind the rapid pace of modern engineering, users frequently seek alternatives to address issues like high costs, lengthy turnaround times, and limited flexibility in testing schedules. When searching for alternatives, consider factors such as pricing structures, the depth of analysis provided, ease of integration with your existing platforms, and the capability to produce audit-ready reports. It’s essential to select a solution that aligns with your team's needs, allowing for efficient remediation and continuous security validation.
