AutoPhish vs RocketShare
Side-by-side comparison to help you choose the right product.
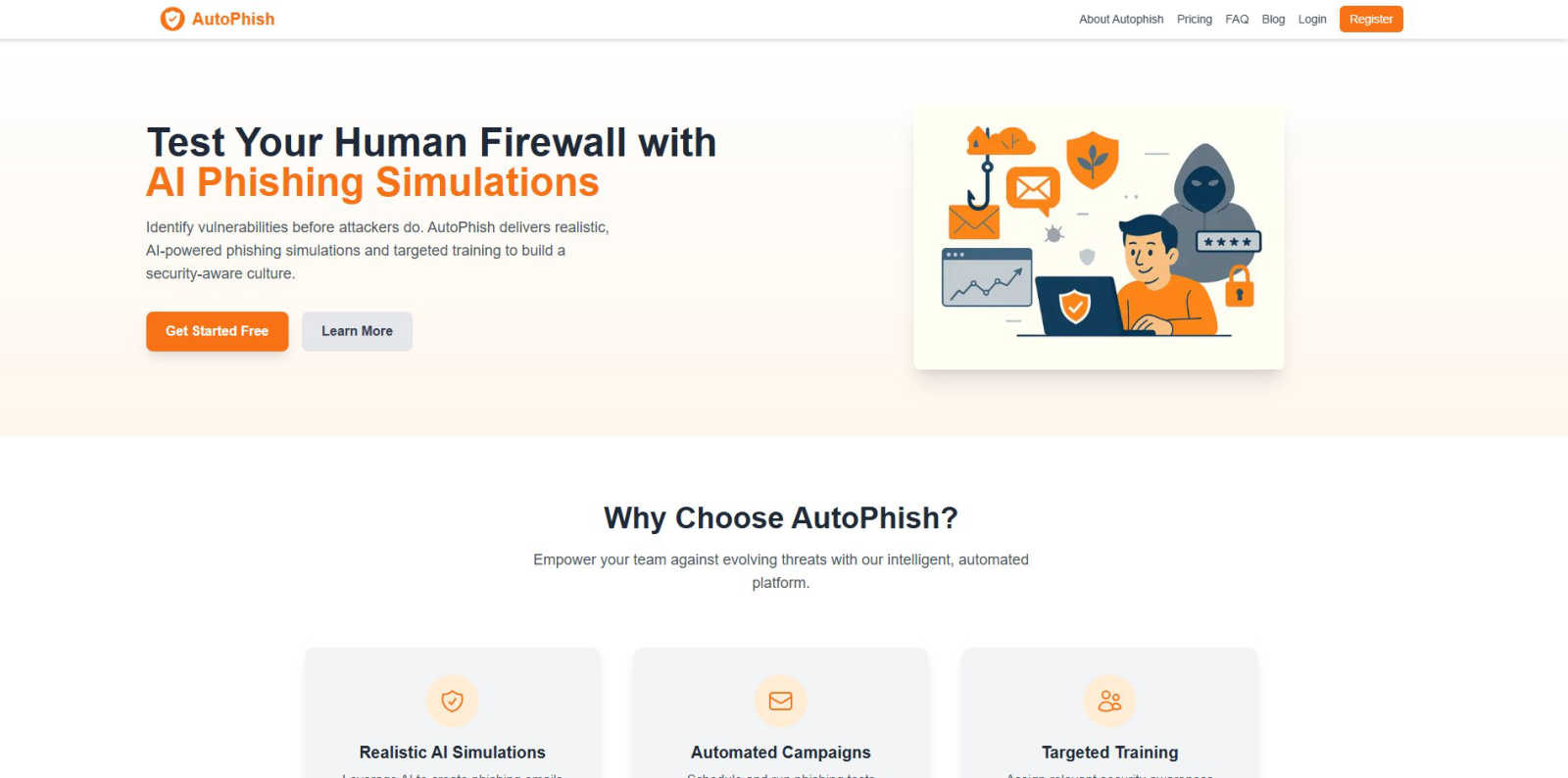
AutoPhish empowers your team with AI-driven phishing simulations to identify vulnerabilities and enhance security.
Last updated: March 1, 2026
RocketShare
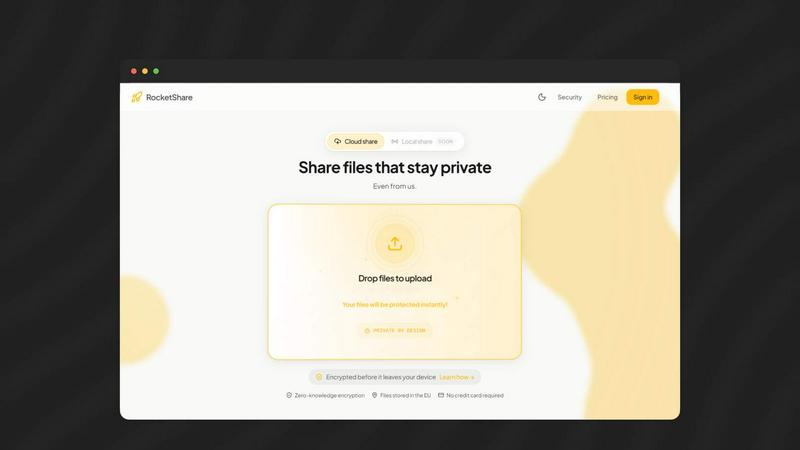
RocketShare enables lightning-fast, private file sharing with zero-knowledge encryption for ultimate security.
Last updated: March 4, 2026
Visual Comparison
AutoPhish
RocketShare
Feature Comparison
AutoPhish
Realistic AI Simulations
AutoPhish harnesses cutting-edge AI technology to create phishing emails that closely mimic actual attacks. These hyper-realistic simulations are tailored to your specific industry, ensuring that your team encounters threats that they are likely to face in real life.
Automated Campaigns
With AutoPhish, you can schedule and run phishing tests automatically, eliminating the need for manual intervention. This feature ensures consistent training and allows your organization to maintain a proactive stance against evolving cyber threats while saving valuable time.
Targeted Training
After users interact with a simulation, AutoPhish's intelligent engine automatically assigns relevant security awareness training based on individual results and roles. This targeted approach enhances the learning experience, ensuring that users receive the specific training they need to strengthen their defenses.
Advanced Reporting
AutoPhish provides advanced reporting capabilities that give you detailed insights into user performance and organizational vulnerabilities. This feature allows you to track progress over time and make informed decisions about future training and testing strategies.
RocketShare
Zero-Knowledge Encryption
RocketShare utilizes a zero-knowledge encryption model, ensuring that files are encrypted on your device immediately upon upload. This means that no one, not even RocketShare, can access your files, preserving your privacy and data integrity.
Cloud-Based and Peer-to-Peer Sharing
The platform offers versatile sharing options, allowing users to choose between cloud-based sharing for convenience or local peer-to-peer transfers for enhanced security. This flexibility accommodates various needs and preferences.
Secure Data Storage in the EU
All files shared via RocketShare are securely stored in the European Union, adhering to strict data protection regulations. This ensures compliance and gives users peace of mind regarding the safety of their sensitive information.
Simple User Interface
RocketShare boasts a beautifully simple and intuitive interface, making file sharing quick and easy. Users can drag and drop files or click to browse, ensuring that even the least tech-savvy individuals can navigate the platform effortlessly.
Use Cases
AutoPhish
Employee Training
Organizations can utilize AutoPhish to conduct regular phishing simulations, helping employees recognize phishing attempts and respond appropriately. This continuous training builds a culture of security awareness among staff.
Incident Response Preparedness
By simulating real-world phishing attacks, AutoPhish prepares teams for potential incidents, ensuring they know how to respond effectively. This proactive approach minimizes the risk of successful attacks and enhances overall incident response strategies.
Risk Assessment
AutoPhish enables organizations to identify vulnerabilities within their workforce. By analyzing simulation results, companies can pinpoint weak areas and implement targeted training to address specific risks.
Compliance Training
With regulatory compliance becoming increasingly critical, organizations can leverage AutoPhish to fulfill training requirements. The platform helps ensure that employees are aware of security protocols and best practices to maintain compliance.
RocketShare
Legal Document Transmission
Law firms can use RocketShare to securely send sensitive case files, ensuring that client data remains confidential and protected from unauthorized access during transmission.
Photography Client Deliveries
Photographers can utilize RocketShare to deliver high-resolution galleries to clients, ensuring that the files remain private and secure, while also providing a seamless delivery experience.
Collaborative Team Projects
Teams working on confidential projects can share documents and files securely through RocketShare, maintaining the integrity of their intellectual property and streamlining collaboration without compromising security.
Healthcare Data Sharing
Healthcare professionals can rely on RocketShare to transfer sensitive patient data securely, ensuring compliance with regulations while protecting patient privacy during file sharing.
Overview
About AutoPhish
AutoPhish is your rapid-response, AI-driven solution designed to empower organizations in the fight against cyber threats. In today’s fast-paced digital landscape, where phishing attacks are increasing in sophistication, AutoPhish stands out as a command center for building a robust human firewall. Tailored specifically for IT teams, security officers, and business leaders, this platform automates security awareness testing and training. It generates hyper-realistic phishing simulations that reflect the exact tactics used by malicious actors, customized to your industry’s unique challenges. By automating the entire campaign lifecycle, AutoPhish enables organizations to run consistent phishing tests without manual overhead, saving critical time and resources. When users engage with a simulation, the intelligent engine quickly identifies vulnerabilities and assigns targeted training, creating a seamless loop of testing and education. This proactive approach cultivates a security-aware culture that strengthens defenses against real threats before they strike.
About RocketShare
RocketShare is an innovative file-sharing platform that prioritizes your privacy above all else. Designed for individuals and businesses alike, it enables users to send files of any size with the assurance that only authorized recipients can access the content. This confidence stems from RocketShare's zero-knowledge encryption model, which ensures that files are encrypted on your device before they ever reach the internet. The encryption key remains with you, often embedded within the share link, meaning that the servers only handle encrypted, unreadable data. Whether you are a lawyer transmitting sensitive legal documents, a photographer delivering high-resolution galleries, or a team collaborating on confidential projects, RocketShare delivers enterprise-grade security in a user-friendly package. With both cloud-based and local peer-to-peer sharing options, and data securely stored in the EU, RocketShare is the ideal solution for anyone valuing simplicity without sacrificing top-tier security.
Frequently Asked Questions
AutoPhish FAQ
What types of phishing simulations does AutoPhish offer?
AutoPhish provides a variety of realistic phishing simulations that mimic real-world attacks. These simulations are tailored to your specific industry, ensuring that your team is prepared for the threats they are likely to encounter.
How does AutoPhish automate the training process?
The platform automatically assigns targeted security awareness training based on the results of each phishing simulation. This ensures that users receive relevant training that addresses their specific vulnerabilities and roles.
Can I customize the phishing tests?
Yes, AutoPhish allows you to configure campaigns by choosing from various templates, targeting specific user groups, and scheduling tests according to your organization’s needs.
Is there a free trial available for AutoPhish?
Yes, AutoPhish offers a free trial, allowing you to get started with phishing simulations without any upfront cost. This enables you to experience the platform's capabilities before committing to a paid plan.
RocketShare FAQ
What is zero-knowledge encryption?
Zero-knowledge encryption is a security model where only the user has access to the encryption key. This ensures that no third party, including the service provider, can access the user's files.
How do I share files using RocketShare?
To share files, simply drag and drop your files into the RocketShare interface or click to browse for files on your device. Your files will be encrypted automatically before upload.
Where is my data stored?
All data shared via RocketShare is securely stored in the European Union, ensuring compliance with stringent data protection regulations and enhancing the security of your files.
Is there a limit on file sizes?
RocketShare allows users to send files of any size, giving you the freedom to share large documents, videos, or images without worrying about size restrictions.
Alternatives
AutoPhish Alternatives
AutoPhish is a cutting-edge platform that leverages AI to automate phishing simulations and security training, designed to fortify organizations against evolving cyber threats. As businesses increasingly recognize the importance of cybersecurity, users often seek alternatives for various reasons, including budget constraints, specific feature requirements, or compatibility with existing systems. When exploring alternatives, it's crucial to consider aspects such as the effectiveness of the phishing simulations, the flexibility of campaign management, and the relevance of assigned training to ensure robust security awareness.
RocketShare Alternatives
RocketShare is a cutting-edge file-sharing platform that prioritizes user privacy through zero-knowledge encryption, ensuring that your data remains completely inaccessible, even to RocketShare itself. It falls under the Productivity & Management category and caters to individuals and businesses that need to share sensitive files securely and efficiently. Users often seek alternatives to RocketShare for various reasons, including pricing, specific feature sets, or compatibility with different platforms. When searching for an alternative, consider factors such as the level of encryption, ease of use, file size limits, and the nature of data storage. Look for a platform that aligns with your specific needs while maintaining robust security measures to protect your sensitive information.

